Implementing the NIST Framework: Best Practices for Long-Term Cybersecurity
Introduction
Cybersecurity is no longer just a concern for large enterprises. Small and mid-sized businesses are increasingly becoming prime targets, often because attackers know their defenses are easier to break. What used to be occasional threats has now turned into constant pressure on operations, budgets, and internal teams.
Many organizations still rely on reactive fixes, addressing issues only after something goes wrong. That approach might have worked in the past, but today it leaves too much room for damage. A more structured, proactive strategy is needed, and that is where established frameworks come into play.
Implementing a cybersecurity framework like NIST gives businesses a clear path forward. It helps turn scattered security efforts into a cohesive system that reduces risk, improves response times, and supports long-term growth. Even without a large internal IT team, companies can build a strong security foundation with the right approach and support.
Key Takeaways
- The NIST CSF provides a flexible, outcome-based blueprint to manage cyber risks, regardless of your business size.
- Achieving long-term resilience requires aligning the right tools and processes with each core NIST function.
- Outsourcing implementation can simplify complex requirements and create a continuous, manageable security cycle.
- Working with experienced IT professionals replaces unpredictable costs with stable, predictable support.
What is the NIST Cybersecurity Framework (CSF)?
At first glance, the idea of a government-backed framework can feel overwhelming. Many assume it comes with rigid rules, complicated audits, and heavy costs. In reality, the NIST Cybersecurity Framework is designed to be practical and adaptable.
Rather than forcing strict compliance, it offers guidance that organizations can tailor to their size and needs. It also creates a shared language, allowing leadership teams and technical staff to align on priorities without getting lost in technical jargon.
The framework is not limited to large corporations. It scales effectively, making it just as valuable for growing businesses that need structure without unnecessary complexity.
The Core Functions of NIST CSF 2.0: A Blueprint for SMBs
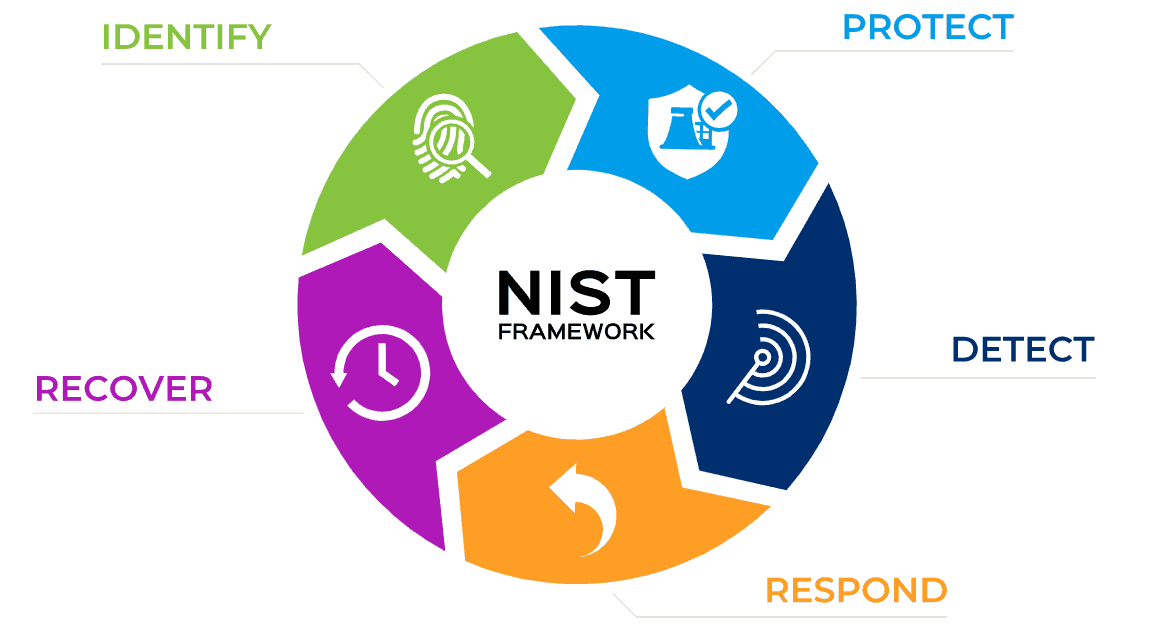
Cybersecurity is not a one-time project. It is an ongoing process that evolves as threats change. The NIST framework reflects this by organizing security into a continuous cycle.
Each function builds on the others, creating a loop of improvement rather than a checklist that gets completed once.
| NIST Function | Practical Goal for SMBs |
| Govern | Establish a clear cybersecurity strategy and assign responsibilities. |
| Identify | Understand assets, risks, and vulnerabilities across your systems. |
| Protect | Implement safeguards to prevent unauthorized access. |
| Detect | Monitor systems to identify suspicious activity quickly. |
| Respond | Act quickly to contain and manage incidents. |
| Recover | Restore operations and data after an incident. |
How to Map IT Infrastructure to NIST Best Practices
Understanding the framework is one thing, but applying it in a real-world environment is where the challenge begins. Each function must connect to practical tools and daily operations.
Govern and Identify: Assessing Your Risks
Every effective security strategy starts with visibility. You need to know what systems you have, where your data lives, and where your weaknesses are.
A structured risk assessment helps uncover outdated systems, misconfigurations, and gaps that attackers could exploit. From there, you can prioritize improvements instead of guessing where to start.
The human factor also plays a major role. Employees are often the first target in phishing or credential-based attacks. Regular training and awareness programs help reduce this risk and turn staff into a line of defense rather than a vulnerability.
Protect and Detect: Strengthening Your Defenses
Once risks are identified, the next step is putting the right protections in place. Traditional antivirus tools are no longer enough on their own.
Modern security solutions focus on behavior, not just known threats. They monitor activity patterns and stop suspicious behavior before it causes damage.
At the same time, detection systems continuously monitor network activity. These tools act as an early warning system, helping teams respond before an issue escalates into a full-scale incident.
Respond and Recover: Building Resilience
Even with strong defenses, no system is completely immune. That is why response and recovery planning are critical.
A clear response plan ensures that when something goes wrong, your team knows exactly what to do. Quick action can limit damage and prevent the issue from spreading.
Reliable backups are equally important. They provide a safety net that allows your business to recover quickly without paying the cost of extended downtime or data loss. Regular testing ensures those backups will actually work when needed.
Overcoming Implementation Challenges for Resource-Strapped Businesses
For many small and mid-sized organizations, the biggest hurdle is not understanding cybersecurity, it is having the resources to implement it properly.
Hiring a full in-house security team is expensive and often unrealistic. At the same time, relying on a small internal team can lead to gaps, burnout, and missed threats.
This is where external support becomes valuable. Many businesses choose to work with providers offering Mississauga managed IT services, which deliver ongoing monitoring, cybersecurity management, and strategic guidance without the cost of building a large internal team.
This approach gives organizations access to experienced professionals while keeping costs predictable. It also ensures that security is consistently maintained instead of being treated as a one-time project.
Conclusion
Cyber threats are not slowing down, and relying on outdated, reactive approaches only increases risk. Businesses need a structured, proactive way to manage cybersecurity, and the NIST framework provides exactly that.
By focusing on continuous improvement and aligning tools with clear objectives, organizations can build a security strategy that grows with them. This reduces uncertainty, improves response times, and protects both operations and reputation.
You do not need a massive internal team to achieve this level of security. With the right strategy and support, even smaller organizations can build a resilient, scalable defense that stands up to modern threats.






